Internet of Things – IoT – Explained
We love to bust jargot wherever we can, so this week, we’re talking about the Internet of Things – IoT. IoT is thrown around all over, and you’re expected to just understand what it is, and how it all works. We’re here to help!
What is IoT?
We all know what the Internet is by now. When the Internet started out, the only devices being connected together were terminals at university campuses. That spread to PCs in our homes, schools and businesses, and now we all have Internet communicators in our pockets. That brings us to the “Things” part of Internet of Things – what is a thing in this context?
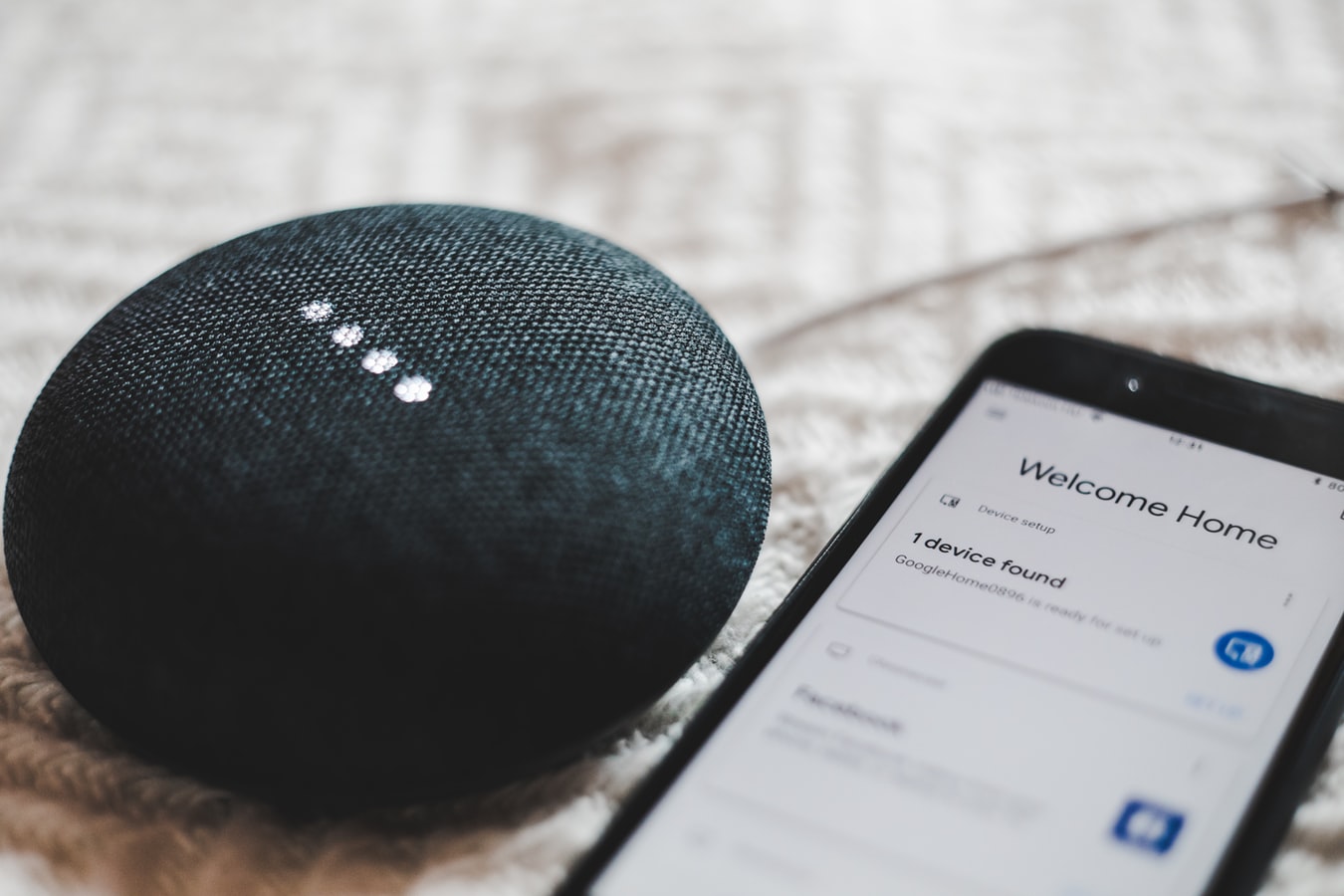
Thermostats, smart speakers, light bulbs, door locks, coffee makers, burglar alrams; the list goes on and on. All of these things can now be connected to the Internet, but they aren’t computers in the usual sense of the word. They’re things.
How do they Connect to the Internet?
Your IoT devices connect to your local wireless network, go through your router, and out of your house, onto the Internet. This is exactly the same as your mobile phone when it is connected to your WiFi. All of these devices exist in one bubble inside your house, all networked together. Whenever any of them need access to the Internet, they ask the router, and it dutifully provides a route for the device to get out onto the web.
But what about getting signals back to the IoT devices from the Internet? You’re on your way home, and you turn the central heating on remotely from your phone – that signal has to get to the heating controller in your house doesn’t it? Without getting too complicated, there are two main ways to make this work;
- The device can use a standard called Universal Plug and Play (UPnP) to tell your router “if traffic turns up here asking for the thermostate, that’s me, so just send it my way please”.
- The device can poll a web service every few minutes. Your phone makes a request to the heating controller’s web services, and the next time your thermostat connects from your house to that web server, it asks if there are any instructions for it, and executes those instructions. Your phone tells the heating control mothership “next time my thermostat checks in, can you ask it to turn the heating on please?” (All Internet communication is very polite in our little world).
IoT Magic!
All this sounds ideal. For the most part, things work the way they’re supposed to, and we all get on brilliantly together. But how can you be sure what your IoT devices are doing with their Internet connections? The short answer is that you can’t.
To be fair, and a bit more balanced about everything, with the complexity of fully fledged computers these days, you could certainly argue that you don’t know what your PC is doing with it’s Internet connection. Remember last time everything was super slow for an hour, and then you got the pop up to say you need to apply updates? Well the computer must have been getting those updates ready while we thought it was just slow, right? We didn’t ask it to do that, but someone programmed it to do that. In the case of software updates, that’s absolutely what we want, but it just goes to show that the computer devices around us are doing as they’re told – and not necessarily as they’re told by us.
So what about the security camera connected to the Internet? It only streams video to us when we tell it to… or does it? How can you be sure?
Sensible Precautions
It is no secret that I am hugely security conscious, to a point. I use the voice assistant on my mobile phone, I have a smart thermostat at home, and I use multi-room speakers connected to the Internet. But I will not have smart speakers in my home, nor will I have connected video cameras.
The reason for drawing the line there is one of consequences. If someone compromises my heating controller, they could make it really warm in my house and cost me a few pounds of gas. Not ideal, but not the end of the world. If someone compromised my speaker system, they could make me listen to worse music than I already have a tase for. Creepy, but again, not earth shattering.
But no matter how much the manufacturer or I try to secure a connected video camera, the fact remains that if it were ever compromised, you’re going to see into my house. I’m not okay with that. The same with smart speakers. The vendors of these amazing products spend a lot of money to keep them secure, and to be fair, they do a terrific job of it. But if they slip up, now you can listen to me anywhere in my house.
Technical Solutions
I won’t go into technical detail here regarding what can be done to mitigate these threats, since there are so many IoT devices around, and the advice would be different for each one, or combination of devices. One really interesting product which caught our eye recently was the Firewalla. Something like a Firewalla is a device which can separate your home network, so you can keep the un-trusted devices off to the side, and keep an eye on what they get upto.
Data Classification
This isn’t a new idea or thought. There are lots of standards around in the business world whereby all data must be classified into different tiers of sensitivity. The most sensitive have ultra stringent security arangements around them, with the obvious trade-off of being laborious processes to follow.
All I’m suggesting is think about the data you’re splashing out around the Internet, and apply reasonable measures to protect that data. Internet of Things devices are super useful, but be mindful that they are devices connected to the Internet, for better or for worse.


